
Key Cyber Security Risk Areas We Help You Manage
Ransomware Risk – Regular backups, strong endpoint protection, network segmentation, and employee awareness.
Data Breach Risk – Access control, encryption, vulnerability testing, and DLP monitoring.
Identity & Access Risk – Multi-factor authentication, least privilege, automated reviews, and account cleanup.
Cloud Security Risk – Encryption, configuration audits, continuous monitoring, and shared responsibility practices.
Compliance Risk – Alignment with standards, regular reviews, automated reporting, and audit readiness.
Incident Response Risk – Tested response plan, 24/7 monitoring, clear escalation, and simulation exercises.
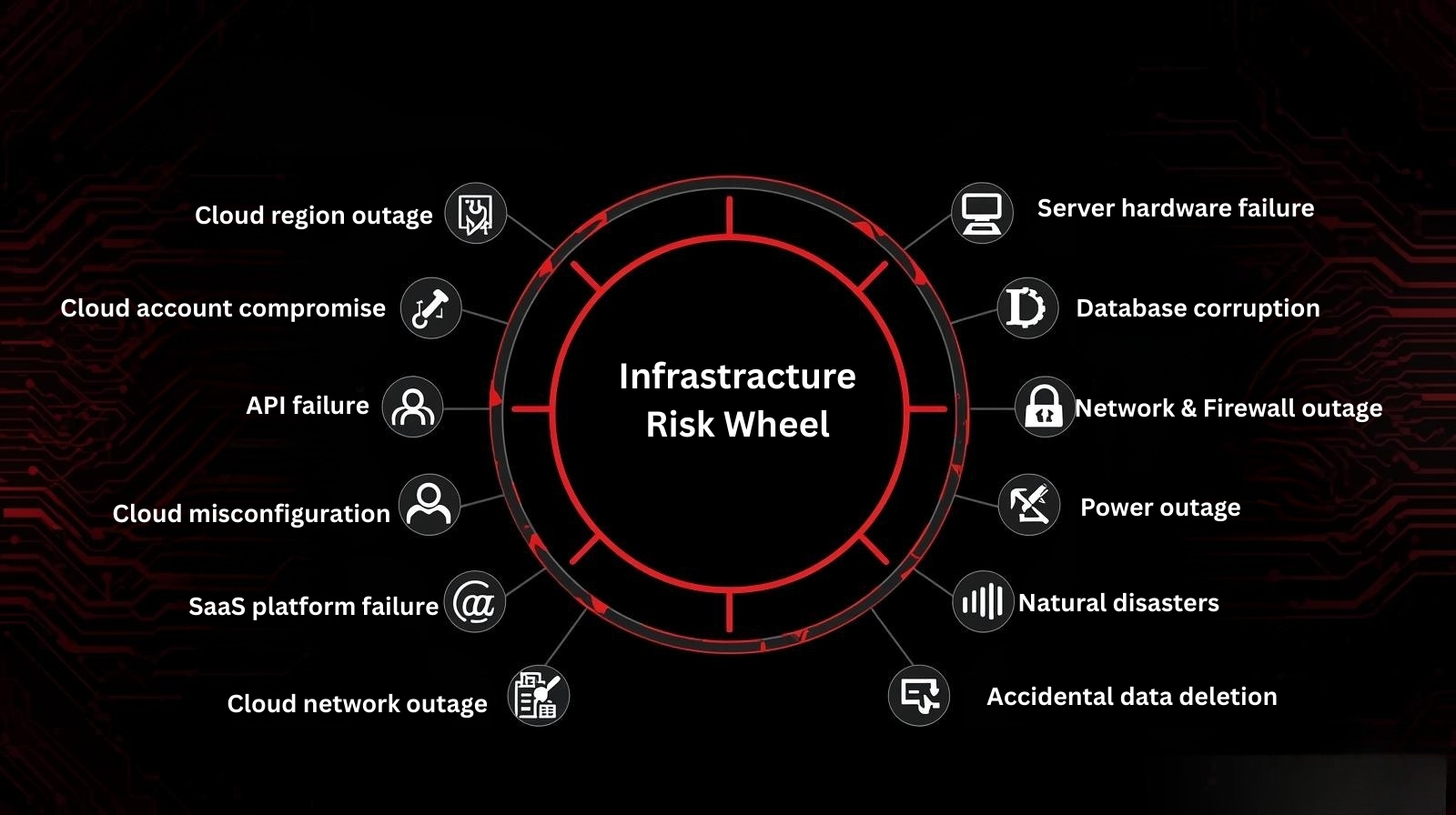
End-to-End Risk Visibility Across Cloud, Infrastructure, Workloads, and Data
Cloud Breach Risk – Secure configurations, encryption, continuous monitoring, and threat detection.
Data Loss Risk – Regular backups, data classification, DLP controls, and secure storage.
Access Compromise Risk – Multi-factor authentication, least privilege, identity governance, and session monitoring.
Service Downtime Risk – High availability design, redundancy, proactive monitoring, and disaster recovery planning.
Compliance Risk – Policy alignment, automated audits, continuous compliance checks, and documentation readiness.
Recovery Failure Risk – Tested recovery plans, backup validation, failover automation, and periodic drills.
Visibility Gap Risk – Unified dashboards, centralized logging, real-time analytics, and continuous asset discovery.
Vendor Exposure Risk – Third-party risk assessments, contract security clauses, continuous monitoring, and vendor compliance reviews.
“Cybercrime is costing the world over $10.5 trillion per year — more than natural disasters, and growing faster than global GDP.”
❌ Slow & unstructured recovery
❌ Human error & dependency
❌ Long downtime (days/weeks)
❌ No guaranteed recovery
❌ Massive financial loss
.png)
Get a Free Assessment and Know Your Risk Today
“We don’t just assess your business continuity — we uncover hidden risks that can cost millions during downtime.”
Business Impact Analysis (BIA) – Identify critical operations and recovery priorities.
Risk & Threat Assessment – Evaluate vulnerabilities and potential disruptions.
IT & Cloud Resilience Review – Measure system strength and recovery capability.
Incident Response & Recovery Readiness – Assess preparedness for cyber and operational incidents.
BCM Compliance & Gap Analysis – Benchmark against ISO 22301 and best practices.
Assessment Report (Free) – Receive a detailed summary of risks and recommendations.
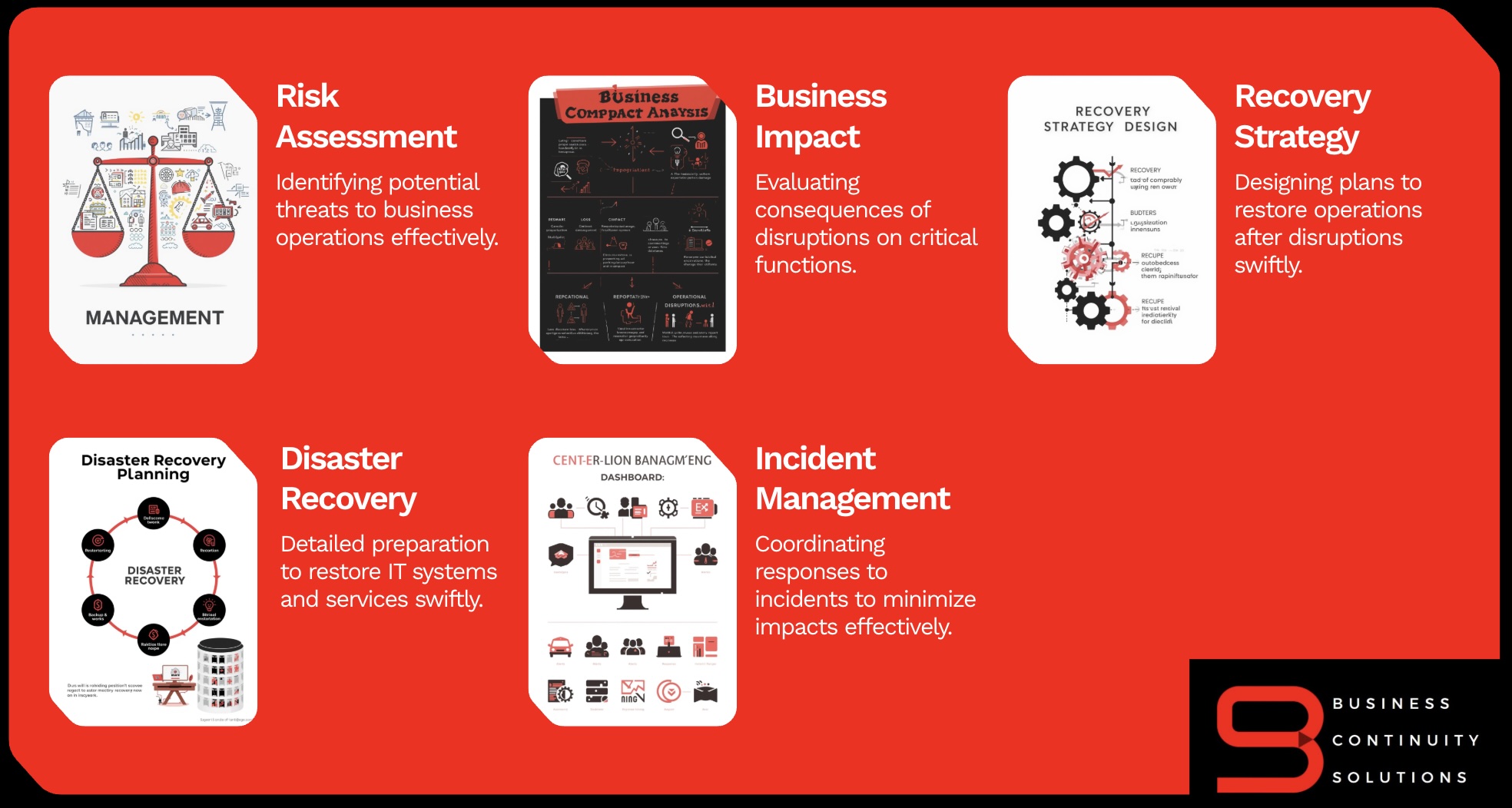
Comprehensive Solutions for Business Continuity
True to our name, we focus on delivering reliable Business Continuity Solutions that help organizations maintain operations during Cyber Attack, Cloud & Infrastructure failures and unexpected disruptions.

From Recovery Chaos to Recovery Made Easy
24/7 Recovery Support – Always-on assistance to restore operations quickly.
Business Continuity Solutions SLA – Guaranteed response and recovery timelines.
24/7 Monitoring Service – Continuous system and risk monitoring for early detection.
Local Support – UAE-based experts ensuring fast, reliable service.
ISO & BCM Training – Certified programs to build internal resilience.
Crisis Communication Tools – Streamlined communication during incidents.
Cybersecurity Specialists – Protection against evolving digital threats.
BCP Specialists – Expert guidance for effective continuity planning.

BIA – Identify critical functions and recovery priorities.
Risk & Gap Analysis – Assess threats and control gaps.
BCP Development – Create tailored continuity strategies.
DR Planning – Define IT recovery for systems and data.
Testing & Simulation – Validate plans through drills.
BCM Governance – Ensure compliance with ISO 22301.
Training & Awareness – Strengthen organizational readiness.
ROC Integration – Link plans with real-time recovery.
1.jpg)
Stay prepared for any operational disruption with advanced ROC solutions in GCC with BCS
At BCS, we partner with industry-leading backup, disaster recovery, and automation technology providers in UAE, Qatar and Saudi Arabia to deliver secure, scalable, and fully automated resilience solutions aligned with ISO 22301 and ISO 27001.
Reasons to Choose BCS for ROC Solutions in UAE
Trusted Expertise – Over a decade of experience delivering reliable Recovery Operations Center (ROC) solutions across the GCC and India.
Comprehensive Backup Partnerships – Strategic alliances with leading backup providers including Veeam, Commvault, Cohesity, Veritas, Rubrik, Arcserve, and Acronis, ensuring flexible, secure, and scalable data protection.
Advanced Replication Technologies – Integration with top replication platforms such as AWS Elastic, Azure Site Recovery, Nutanix, Carbonite, and Zerto for seamless business continuity and rapid recovery.
End-to-End Continuity – Unified solutions covering backup, replication, monitoring, and recovery to minimize downtime and data loss.
Local Presence, Global Standards – UAE-based operations supported by international best practices and certified professionals.
Proven Reliability – Trusted by enterprises for high availability, compliance readiness, and operational resilience.
.jpg)

Cyber Attacks – Malicious attempts to breach systems, steal data, or disrupt operations. Ransomware – A type of malware that encrypts data and demands payment for its release. Data ...
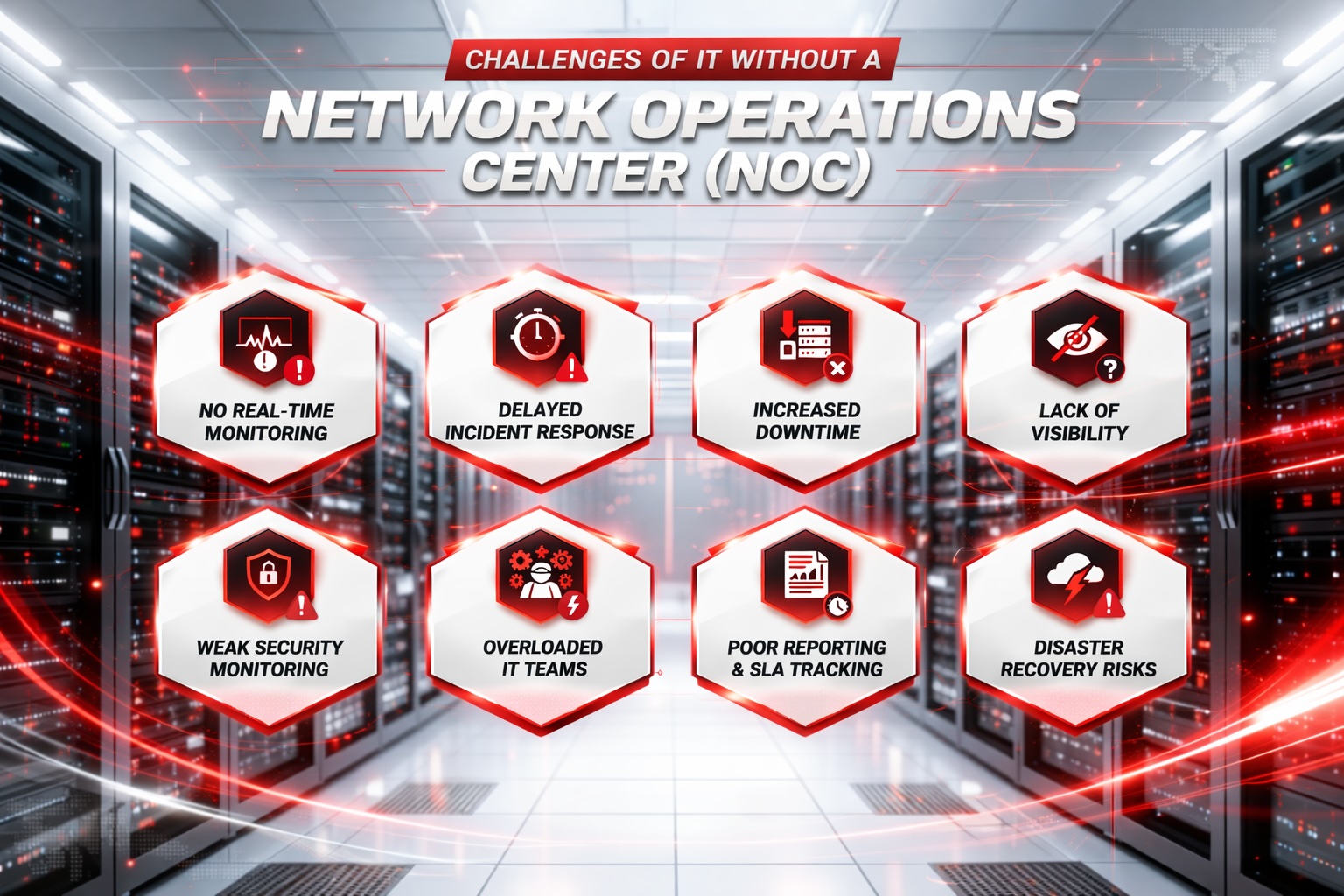
- No Real-Time Monitoring: Issues go unnoticed until they escalate. - Delayed Response: Slower detection and resolution of incidents. - More Downtime: Longer outages impact productivity and reve...
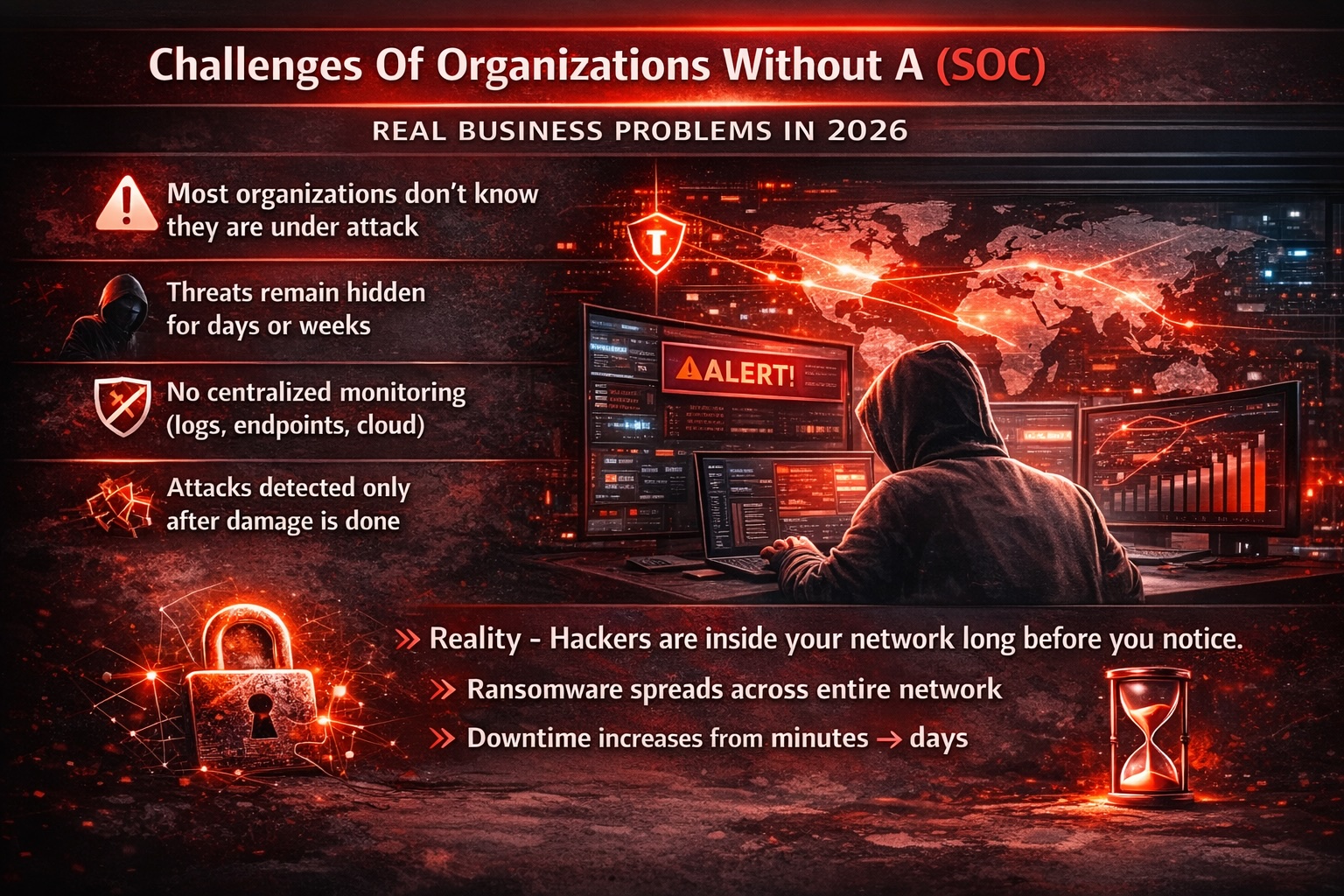
SOC Solutions to Protect Your Business “Your 24/7 Security Shield Against Modern Cyber Threats.” Centralized Security Visibility – Unified monitoring across all systems and ...

Enabling Business Transformation through Managed IT Services Experience a catalyst for business transformation with our cutting-edge Managed IT Services. Leveraging innovative technology solutions and...