SOC Solutions to Protect Your Business
“Your 24/7 Security Shield Against Modern Cyber Threats.”
Centralized Security Visibility – Unified monitoring across all systems and environments.
Real-Time AI Threat Detection – Intelligent analytics to identify and stop attacks instantly.
Rapid Incident Response – Swift containment and remediation to minimize impact.
Proactive Threat Hunting – Continuous search for hidden and emerging threats.
24/7 Security Monitoring – Around-the-clock protection by certified analysts.
Advanced Endpoint & Network Protection – Defense against malware, intrusions, and exploits.
Cloud & Hybrid Security – Secure workloads across on-premises and cloud platforms.
Ransomware & Data Protection – Prevent, detect, and recover from ransomware attacks.
AI-Driven Automation – Accelerated response and reduced manual intervention.
Business Continuity Integration – Seamless alignment with continuity and recovery strategies.
AI-Powered Cyber Attacks (Biggest Shift) – Attackers leveraging AI for automation, evasion, and precision targeting.
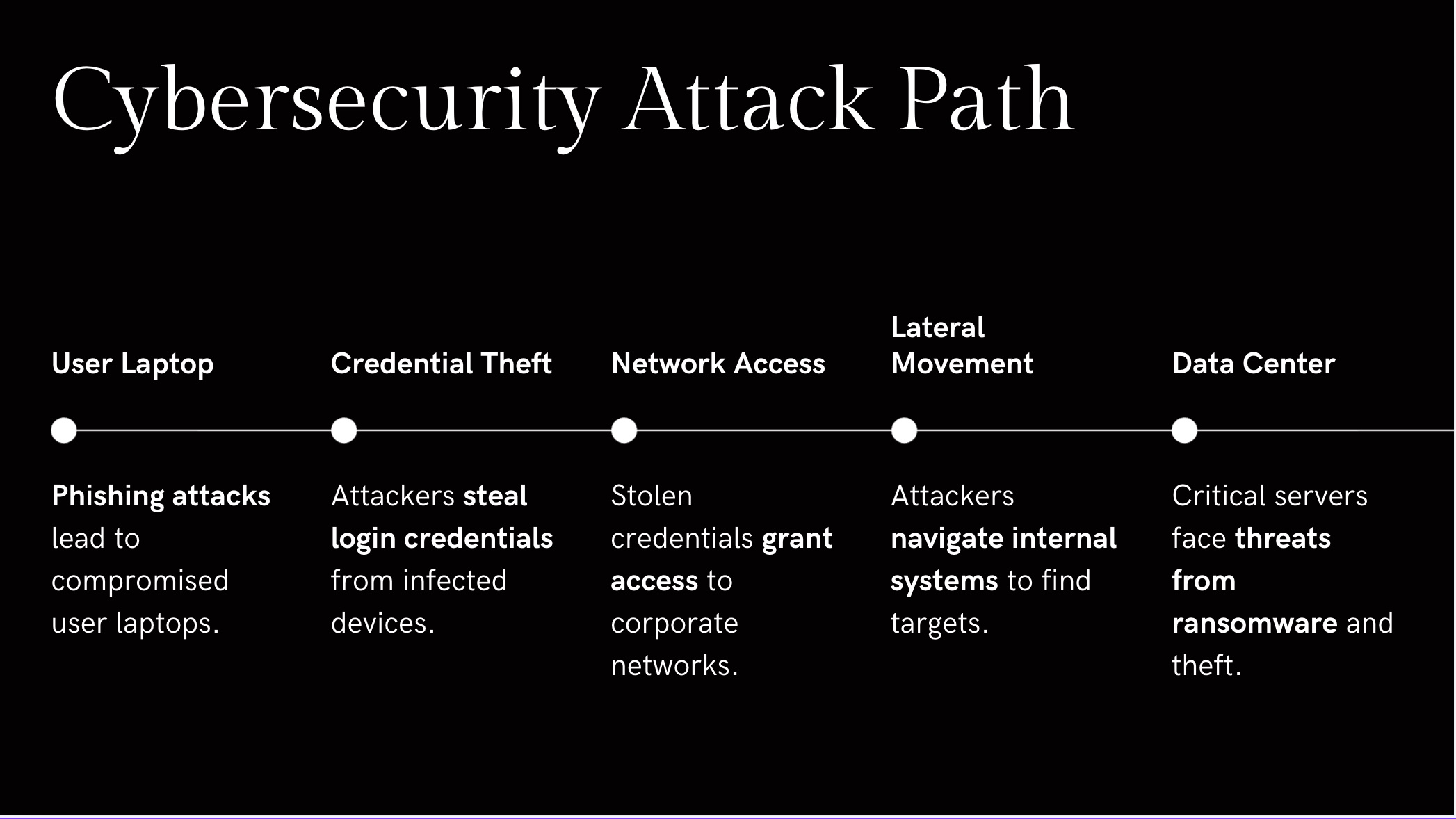
AI-Driven Phishing & BEC – Deepfake and generative AI used to craft convincing phishing and business email compromise campaigns.
Supply Chain Attacks (Critical Risk) – Exploiting third-party vendors and software dependencies to infiltrate trusted networks.
DDoS & Botnet Attacks (Mass Scale) – Large-scale disruptions targeting cloud, financial, and government infrastructure.
Critical Infrastructure & Emerging Threats – Increased targeting of energy, healthcare, and transportation systems.
Geopolitical Cyber Warfare – State-sponsored attacks escalating due to global tensions and digital espionage.
Ransomware Attacks – More sophisticated encryption, double extortion, and data destruction tactics.
Financial & Data Breaches – Rising theft of sensitive data and financial fraud through compromised systems.

An employee clicks a fake email → enters a password → attacker gains access.
Solution for DDoS Attacks
Solution for System Disruptions
With BCS Solutions, the Business Impact
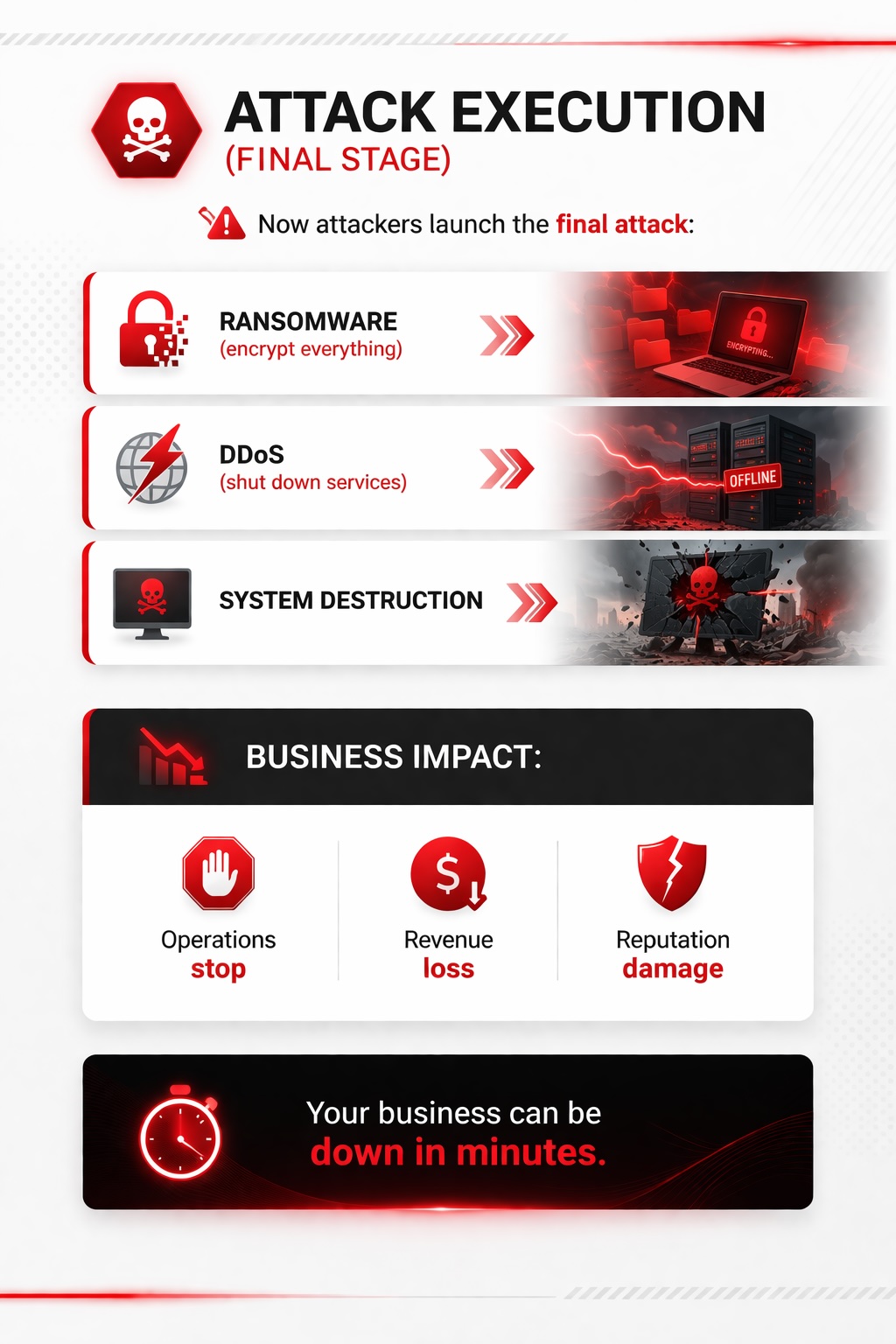
Modern cyber attacks can spread across networks in under 30 minutes - without 24/7 monitoring, most businesses detect them too late.
Don’t wait Act now

Continuous, Real-Time Monitoring
Incident Response & Recovery

AI-Powered Threat Intelligence

Compliance & Security Governance
BCS Integrated Protection Approach
✔ 24/7 Security Operations Center (SOC) in UAE
✔ Real-time threat detection & response
✔ Integrated NOC + SOC + Disaster Recovery
✔ AI-driven monitoring & automation
✔ Compliance with ISO & BCM standards
✔ Centralized visibility (logs, endpoints, cloud)
✔ Faster incident response (minutes vs days)

Identify vulnerabilities, evaluate your current security posture, and strengthen your defenses with a complimentary security assessment from BCS. Our experts analyze your IT environment to uncover risks and provide actionable recommendations to enhance resilience.
Empower your business with proactive security — before threats strike.
.jpg)
Stay ahead of evolving cyber threats with BCS's advanced SOC solutions in UAE. At BCS, our SOC delivers 24/7 real-time monitoring, AI-driven threat detection, and rapid incident response - ensuring your business stays secure and operational at all times.
“While you focus on your business, BCS SOC continuously monitors, detects, and protects your environment - 24/7.”


Cyber Attacks – Malicious attempts to breach systems, steal data, or disrupt operations. Ransomware – A type of malware that encrypts data and demands payment for its release. Data ...
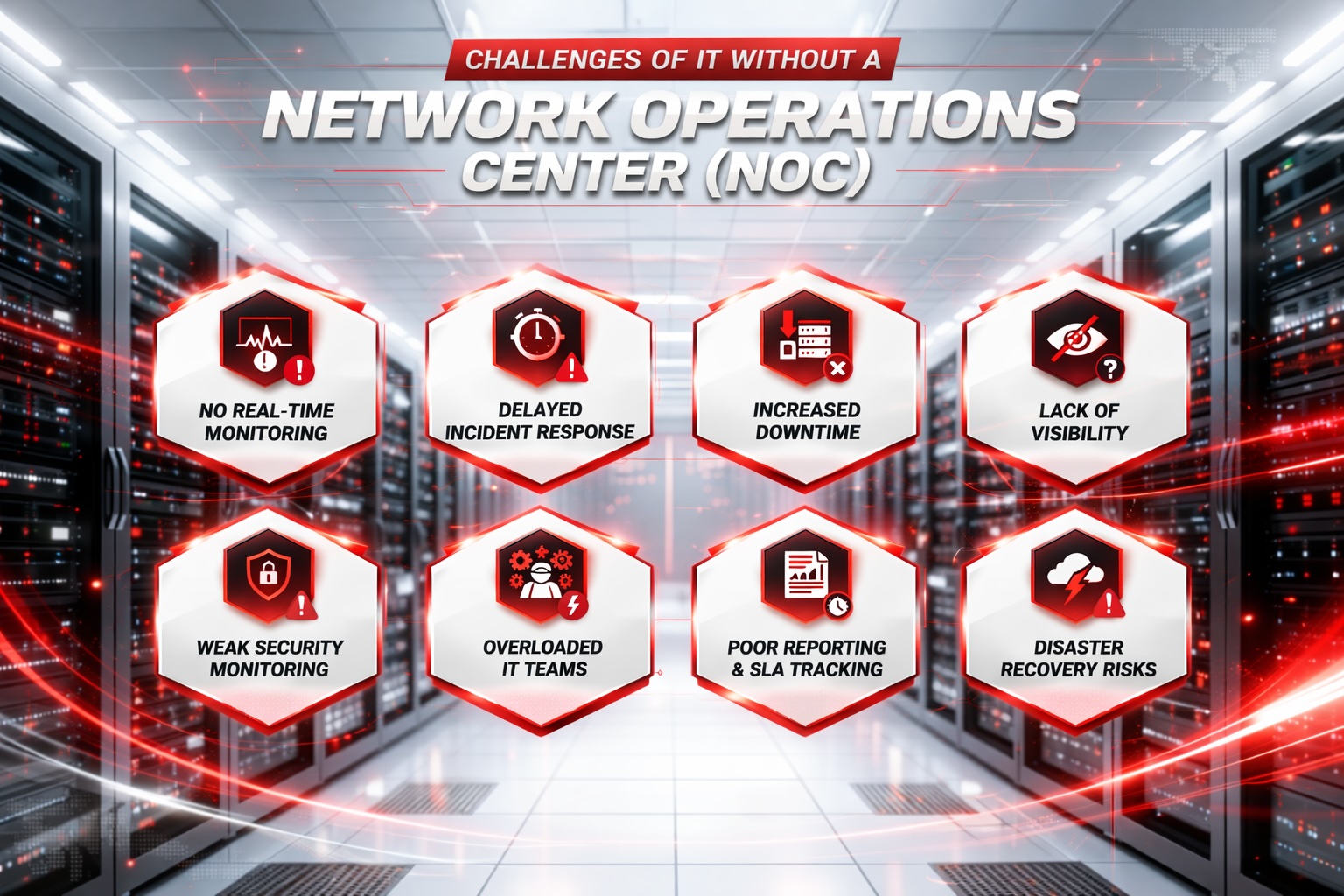
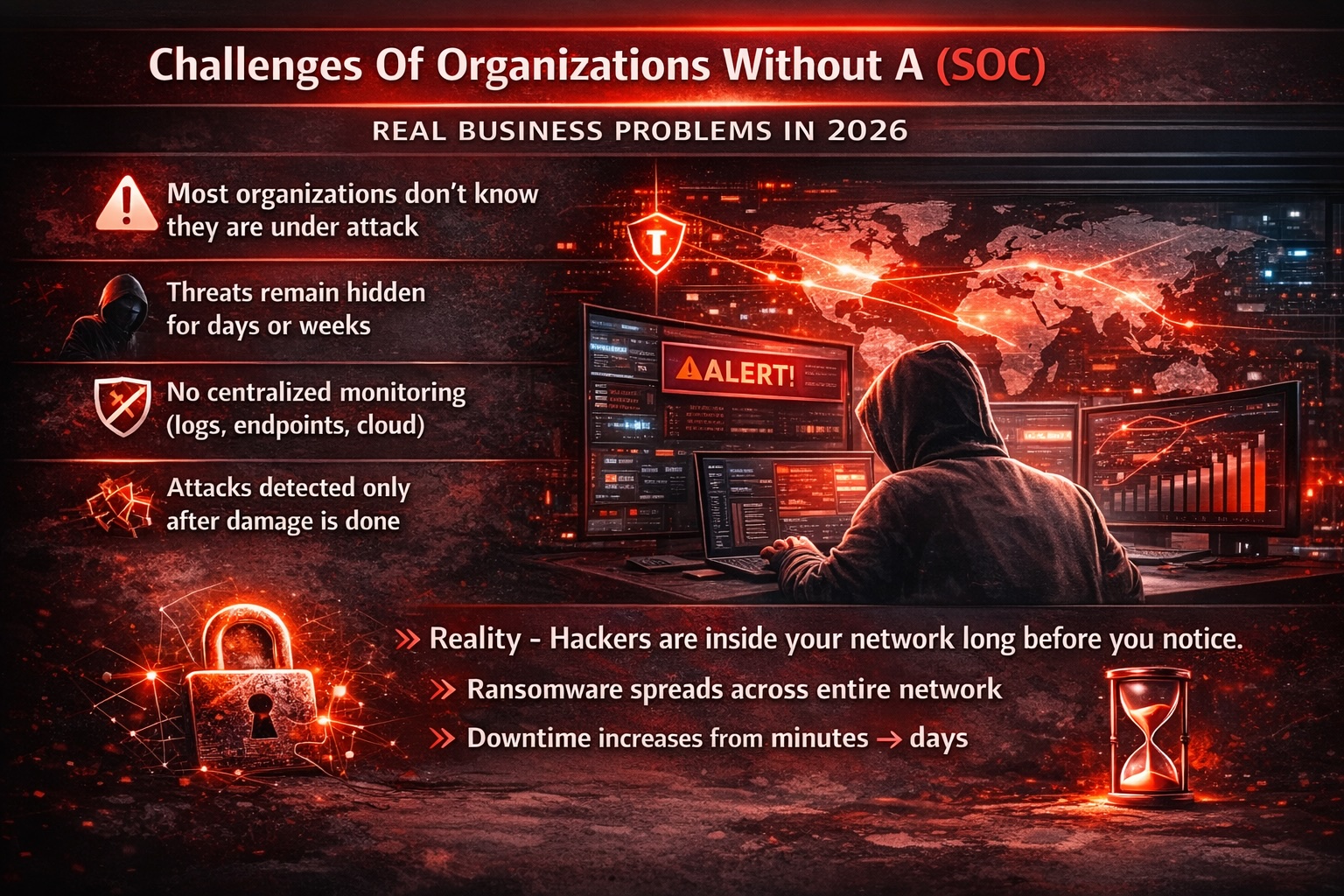
- No Real-Time Monitoring: Issues go unnoticed until they escalate. - Delayed Response: Slower detection and resolution of incidents. - More Downtime: Longer outages impact productivity and reve...

Key Cyber Security Risk Areas We Help You Manage Ransomware Risk – Regular backups, strong endpoint protection, network segmentation, and employee awareness. Data Breach Risk – Acces...

Enabling Business Transformation through Managed IT Services Experience a catalyst for business transformation with our cutting-edge Managed IT Services. Leveraging innovative technology solutions and...