
In today‘s dynamic digital landscape, having robust ITSM and ITAM practices in place is essential. This integrated approach empowers you to handle service requests, incidents, and changes seamlessly, while also maintaining complete control over your IT assets.
IT Service Management (ITSM) involves the implementation and management of IT services to meet the needs of an organization and its customers. It focuses on delivering value to customers through the design, delivery, and continuous improvement of IT services. On the other hand, IT Asset Management (ITAM) is the systematic management of an organization‘s hardware, software, and digital assets throughout their lifecycle. It encompasses procurement, deployment, maintenance, and disposal, with the goal of maximizing asset utilization, minimizing costs, ensuring compliance, and enhancing overall operational efficiency.











Cyber Attacks – Malicious attempts to breach systems, steal data, or disrupt operations. Ransomware – A type of malware that encrypts data and demands payment for its release. Data ...
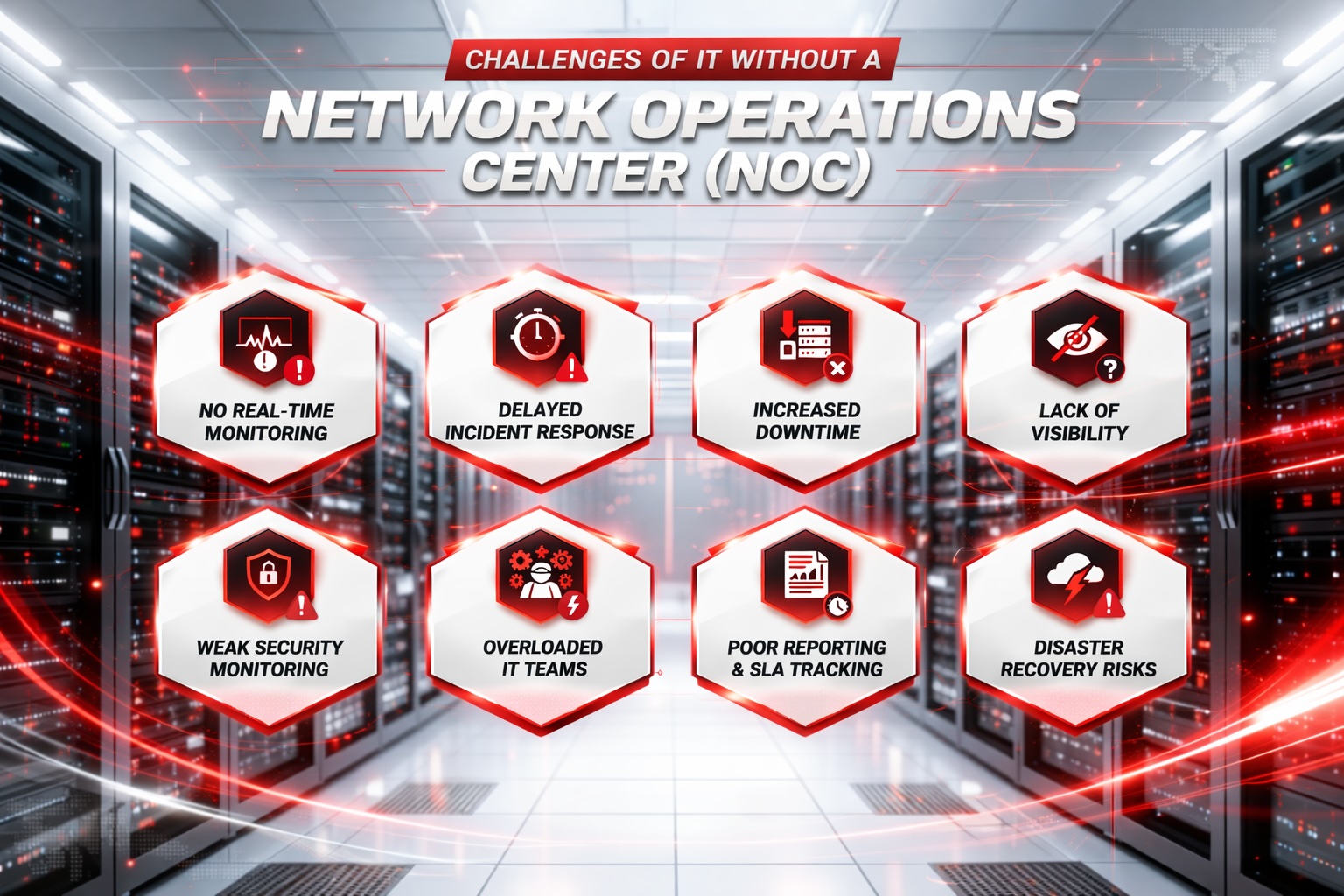
- No Real-Time Monitoring: Issues go unnoticed until they escalate. - Delayed Response: Slower detection and resolution of incidents. - More Downtime: Longer outages impact productivity and reve...
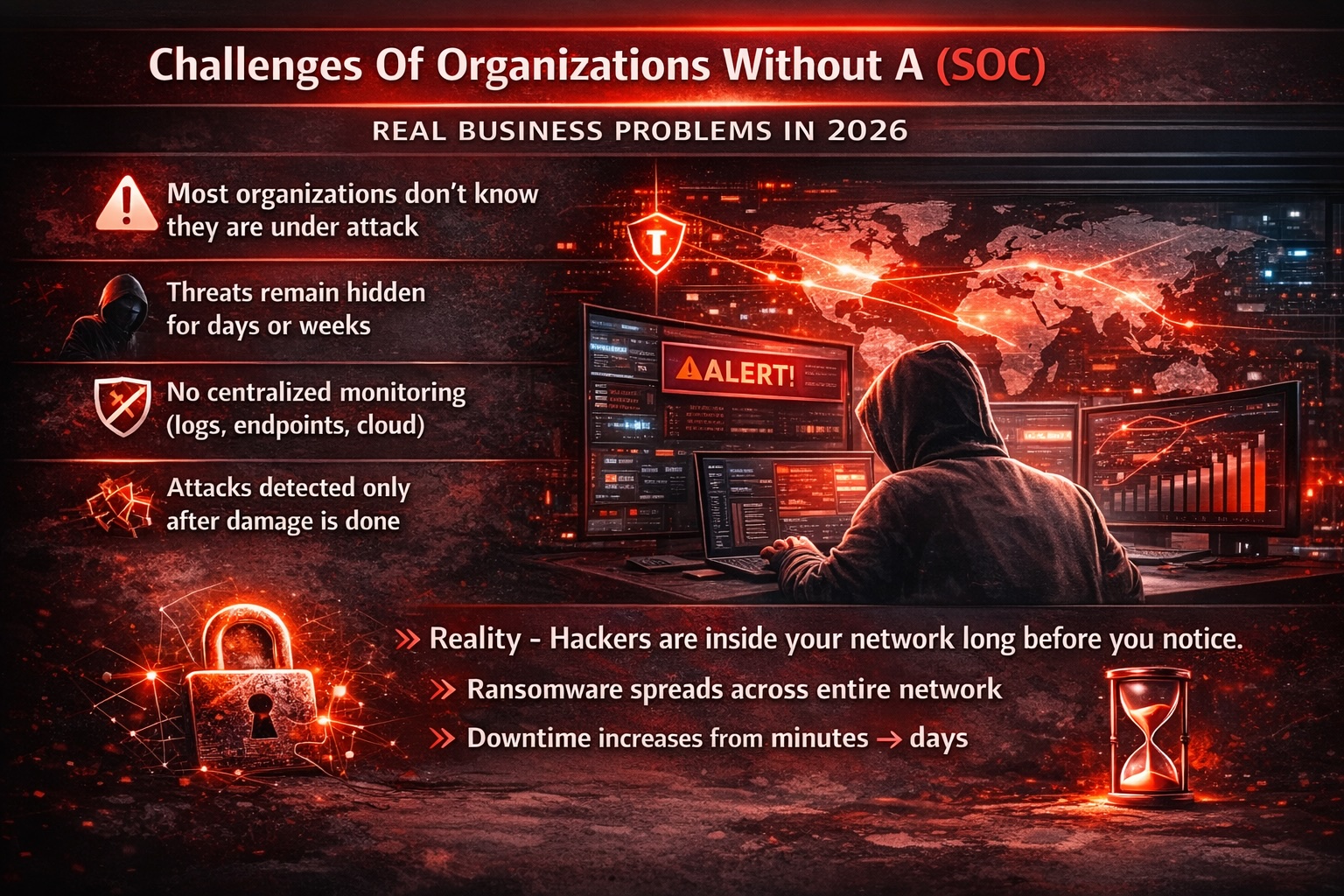
SOC Solutions to Protect Your Business “Your 24/7 Security Shield Against Modern Cyber Threats.” Centralized Security Visibility – Unified monitoring across all systems and ...

Key Cyber Security Risk Areas We Help You Manage Ransomware Risk – Regular backups, strong endpoint protection, network segmentation, and employee awareness. Data Breach Risk – Acces...